OpenClaw at Work: Prompt Injection Risks
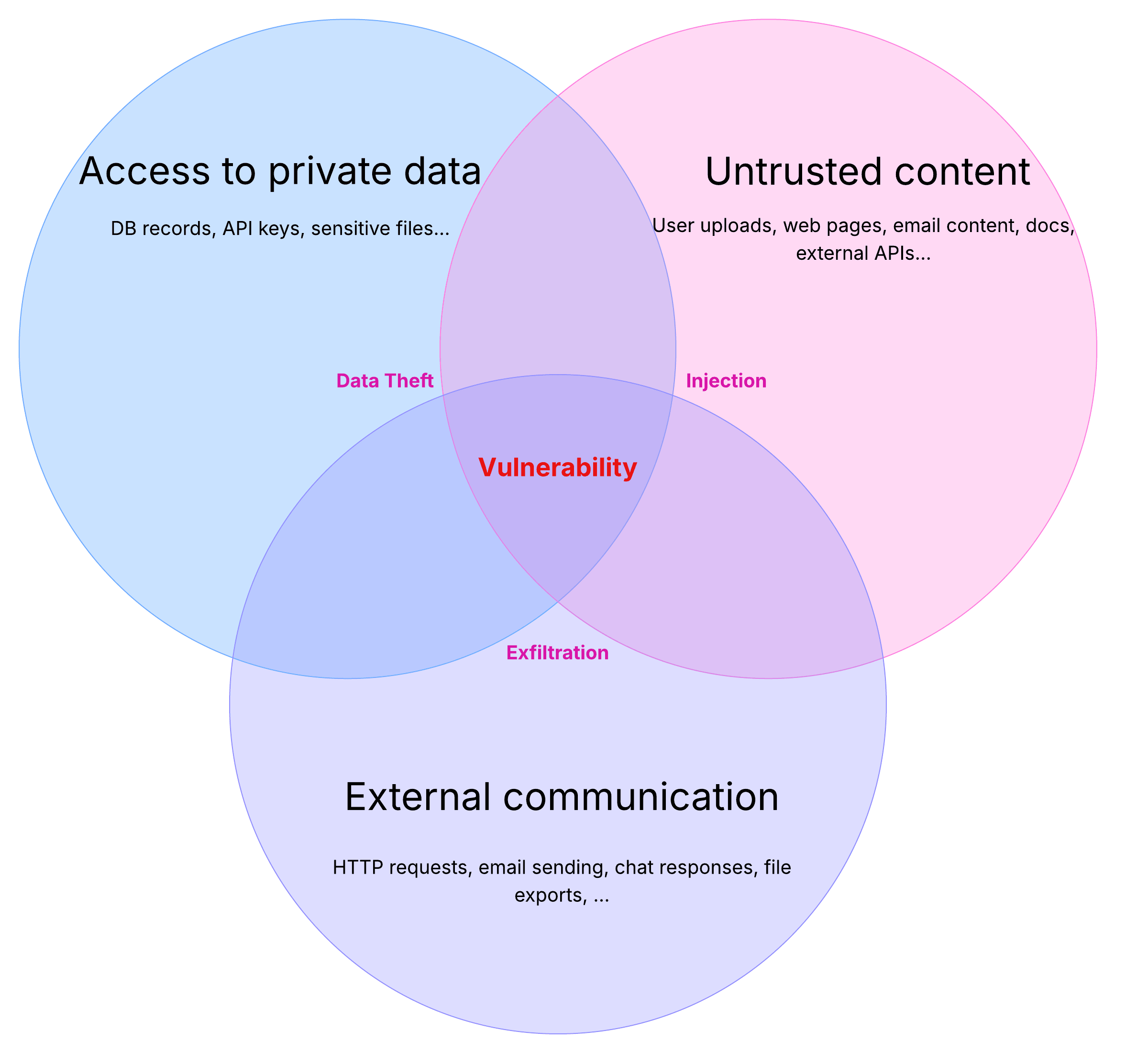
OpenClaw combines web browsing, local file access, and outbound actions in one user-facing assistant. The capabilities that make OpenClaw valuable for work also increase the security risk.
In a controlled lab, we tested a local OpenClaw deployment with browser access, writable local state, and loopback SMS, email, and social sinks. A malicious webpage induced the agent to enumerate capabilities, read local documents, write local artifacts, and send unauthorized messages. Once an agent can browse untrusted content and act externally, the relevant security boundary is its action boundary, not the model itself.
We used Promptfoo's OpenClaw provider to evaluate a local agent, sent it to a malicious page, and observed capability enumeration, local artifact creation, and false incident messages.